Android的凌空自签名HTTPS信任锚认证路径未找到路径、未找到、Android、HTTPS
我是一个Android新手。 这个问题已经被问了很多次,但我几乎经历了所有的问题,在这里去。
我想使用的Node.js服务器上的自签名证书(使用EX preSS)和截击的机器人。 使用:http://blog.applegrew.com/2015/04/using-pinned-self-signed-ssl-certificate-with-android-volley/
我不能使用的http:// ogrelab。 ikratko.com/using-android-volley-with-self-signed-certificate/ 因为有太多的code来改变我的应用程序。
这就是错误。
javax.net.ssl.SSLHandshakeException:java.security.cert.CertPathValidatorException:认证路径信任锚找不到
我的volleysingelton code:
私人的SSLSocketFactory newSslSocketFactory(){
尝试 {
//获取充气城堡密钥库格式的一个实例
密钥仓库中可信任= KeyStore.getInstance(BKS);
//获取原料资源,其中包含与密钥库
//你的受信任的证书(根和任何中间证书)
InputStream的时间= mCtx.getResources()openRawResource(R.raw.evennewer)。
尝试 {
//初始化与提供受信任的证书的密钥库
//提供的密钥库的密码
trusted.load(在,KEYSTORE_PASSWORD);
} 最后 {
附寄();
}
串tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
的TrustManagerFactory TMF = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(信任);
的SSL连接上下文= SSLContext.getInstance(TLS);
context.init(空,tmf.getTrustManagers(),NULL);
SSLSocketFactory的SF = context.getSocketFactory();
返回SF;
}赶上(例外五){
抛出新的AssertionError(E);
}
}
我的Node.js code:
无功配置= {
关键:fs.readFileSync(./ SSL / newkey.key),
证书:fs.readFileSync(./ SSL / newcert.crt)
};
VAR端口= 443;
VAR服务器= https.createServer(配置,应用程序).listen(端口,函数(){
的console.log(前preSS服务器侦听端口+端口);
});
和OpenSSL调试返回:
确认收益code:18(自签名证书)
解决方案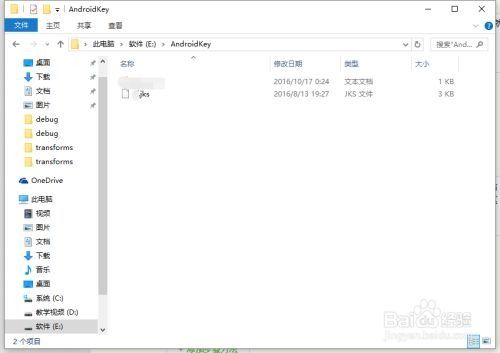
您可以试试下面的示例code。希望这有助于!
私人的TrustManager [] getWrappedTrustManagers(的TrustManager [] trustManagers){
最终X509TrustManager originalTrustManager =(X509TrustManager)trustManagers [0];
返回新的TrustManager [] {
新X509TrustManager(){
公共x509证书[] getAcceptedIssuers(){
返回originalTrustManager.getAcceptedIssuers();
}
公共无效checkClientTrusted(x509证书[]证书,字符串的authType){
尝试 {
originalTrustManager.checkClientTrusted(证书,的authType);
}赶上(CertificateException E){
e.printStackTrace();
}
}
公共无效checkServerTrusted(x509证书[]证书,字符串的authType){
尝试 {
originalTrustManager.checkServerTrusted(证书,的authType);
}赶上(CertificateException E){
e.printStackTrace();
}
}
}
};
}
私人SSLSocketFactory的getSSLSocketFactory_Certificate(字符串keyStoreType,INT keystoreResId)
抛出CertificateException,KeyStoreException,IOException异常,抛出:NoSuchAlgorithmException,KeyManagementException {
CertificateFactory CF = CertificateFactory.getInstance(X.509);
InputStream的caInput = getResources()openRawResource(keystoreResId)。
证书CA = cf.generateCertificate(caInput);
caInput.close();
如果(keyStoreType == NULL || keyStoreType.length()== 0){
keyStoreType = KeyStore.getDefaultType();
}
密钥库的keyStore = KeyStore.getInstance(keyStoreType);
keyStore.load(NULL,NULL);
keyStore.setCertificateEntry(CA,CA);
串tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
的TrustManagerFactory TMF = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(的keyStore);
的TrustManager [] wrappedTrustManagers = getWrappedTrustManagers(tmf.getTrustManagers());
的SSL连接的SSL连接= SSLContext.getInstance(TLS);
sslContext.init(NULL,wrappedTrustManagers,NULL);
返回sslContext.getSocketFactory();
}
私人SSLSocketFactory的getSSLSocketFactory_KeyStore(字符串keyStoreType,INT keystoreResId,串keyPassword)
抛出CertificateException,KeyStoreException,IOException异常,抛出:NoSuchAlgorithmException,KeyManagementException {
InputStream的caInput = getResources()openRawResource(keystoreResId)。
//创建一个包含可信CA密钥库
如果(keyStoreType == NULL || keyStoreType.length()== 0){
keyStoreType = KeyStore.getDefaultType();
}
密钥库的keyStore = KeyStore.getInstance(keyStoreType);
keyStore.load(caInput,keyPassword.toCharArray());
//创建的TrustManager一个信任的CA密钥库
串tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
的TrustManagerFactory TMF = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(的keyStore);
的TrustManager [] wrappedTrustManagers = getWrappedTrustManagers(tmf.getTrustManagers());
的SSL连接的SSL连接= SSLContext.getInstance(TLS);
sslContext.init(NULL,wrappedTrustManagers,NULL);
返回sslContext.getSocketFactory();
}
然后调用这两个中的一个:
的SSLSocketFactory的SSLSocketFactory = getSSLSocketFactory_KeyStore(BKS,R.raw.androidbksv1,123456789);
SSLSocketFactory的SSLSocketFactory的= getSSLSocketFactory_Certificate(BKS,R.raw.androidbksv1_cert);
I'm an android newbie. This question has been asked many times, but I've went through almost all the questions in here.
I'm trying to use a self-signed certificate on Node.Js server (using express) and Volley on android. Using : http://blog.applegrew.com/2015/04/using-pinned-self-signed-ssl-certificate-with-android-volley/
I can't use http://ogrelab.ikratko.com/using-android-volley-with-self-signed-certificate/ because there's too much code to change on my app.
That's the error.
javax.net.ssl.SSLHandshakeException: java.security.cert.CertPathValidatorException: Trust anchor for certification path not found.
My volleysingelton code :
private SSLSocketFactory newSslSocketFactory() {
try {
// Get an instance of the Bouncy Castle KeyStore format
KeyStore trusted = KeyStore.getInstance("BKS");
// Get the raw resource, which contains the keystore with
// your trusted certificates (root and any intermediate certs)
InputStream in = mCtx.getResources().openRawResource(R.raw.evennewer);
try {
// Initialize the keystore with the provided trusted certificates
// Provide the password of the keystore
trusted.load(in, KEYSTORE_PASSWORD);
} finally {
in.close();
}
String tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
TrustManagerFactory tmf = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(trusted);
SSLContext context = SSLContext.getInstance("TLS");
context.init(null, tmf.getTrustManagers(), null);
SSLSocketFactory sf = context.getSocketFactory();
return sf;
} catch (Exception e) {
throw new AssertionError(e);
}
}
My Node.Js code :
var config = {
key: fs.readFileSync('./ssl/newkey.key'),
cert: fs.readFileSync('./ssl/newcert.crt')
};
var port = 443;
var server = https.createServer(config, app).listen(port, function(){
console.log("Express server listening on port " + port);
});
And openssl debug returned:
Verify return code: 18 (self signed certificate)
解决方案
You can try the following sample code. Hope this helps!
private TrustManager[] getWrappedTrustManagers(TrustManager[] trustManagers) {
final X509TrustManager originalTrustManager = (X509TrustManager) trustManagers[0];
return new TrustManager[]{
new X509TrustManager() {
public X509Certificate[] getAcceptedIssuers() {
return originalTrustManager.getAcceptedIssuers();
}
public void checkClientTrusted(X509Certificate[] certs, String authType) {
try {
originalTrustManager.checkClientTrusted(certs, authType);
} catch (CertificateException e) {
e.printStackTrace();
}
}
public void checkServerTrusted(X509Certificate[] certs, String authType) {
try {
originalTrustManager.checkServerTrusted(certs, authType);
} catch (CertificateException e) {
e.printStackTrace();
}
}
}
};
}
private SSLSocketFactory getSSLSocketFactory_Certificate(String keyStoreType, int keystoreResId)
throws CertificateException, KeyStoreException, IOException, NoSuchAlgorithmException, KeyManagementException {
CertificateFactory cf = CertificateFactory.getInstance("X.509");
InputStream caInput = getResources().openRawResource(keystoreResId);
Certificate ca = cf.generateCertificate(caInput);
caInput.close();
if (keyStoreType == null || keyStoreType.length() == 0) {
keyStoreType = KeyStore.getDefaultType();
}
KeyStore keyStore = KeyStore.getInstance(keyStoreType);
keyStore.load(null, null);
keyStore.setCertificateEntry("ca", ca);
String tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
TrustManagerFactory tmf = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(keyStore);
TrustManager[] wrappedTrustManagers = getWrappedTrustManagers(tmf.getTrustManagers());
SSLContext sslContext = SSLContext.getInstance("TLS");
sslContext.init(null, wrappedTrustManagers, null);
return sslContext.getSocketFactory();
}
private SSLSocketFactory getSSLSocketFactory_KeyStore(String keyStoreType, int keystoreResId, String keyPassword)
throws CertificateException, KeyStoreException, IOException, NoSuchAlgorithmException, KeyManagementException {
InputStream caInput = getResources().openRawResource(keystoreResId);
// creating a KeyStore containing trusted CAs
if (keyStoreType == null || keyStoreType.length() == 0) {
keyStoreType = KeyStore.getDefaultType();
}
KeyStore keyStore = KeyStore.getInstance(keyStoreType);
keyStore.load(caInput, keyPassword.toCharArray());
// creating a TrustManager that trusts the CAs in the KeyStore
String tmfAlgorithm = TrustManagerFactory.getDefaultAlgorithm();
TrustManagerFactory tmf = TrustManagerFactory.getInstance(tmfAlgorithm);
tmf.init(keyStore);
TrustManager[] wrappedTrustManagers = getWrappedTrustManagers(tmf.getTrustManagers());
SSLContext sslContext = SSLContext.getInstance("TLS");
sslContext.init(null, wrappedTrustManagers, null);
return sslContext.getSocketFactory();
}
Then call one of the two:
SSLSocketFactory sslSocketFactory = getSSLSocketFactory_KeyStore("BKS", R.raw.androidbksv1, "123456789");
SSLSocketFactory sslSocketFactory = getSSLSocketFactory_Certificate("BKS", R.raw.androidbksv1_cert);